Industrial automation is currently facing a significant security inflection point. As of early May 2026, the Cybersecurity and Infrastructure Security Agency (CISA) has issued a series of critical advisories targeting one of the most bedrock components of modern manufacturing: the Rockwell Automation Allen-Bradley ControlLogix platform. This is not just another routine patch warning; it is a federal mandate with active exploitation already observed in the field, requiring industrial operators to take decisive action by the end of this month.
The 2026 Rockwell Security Crisis: What is at Stake?
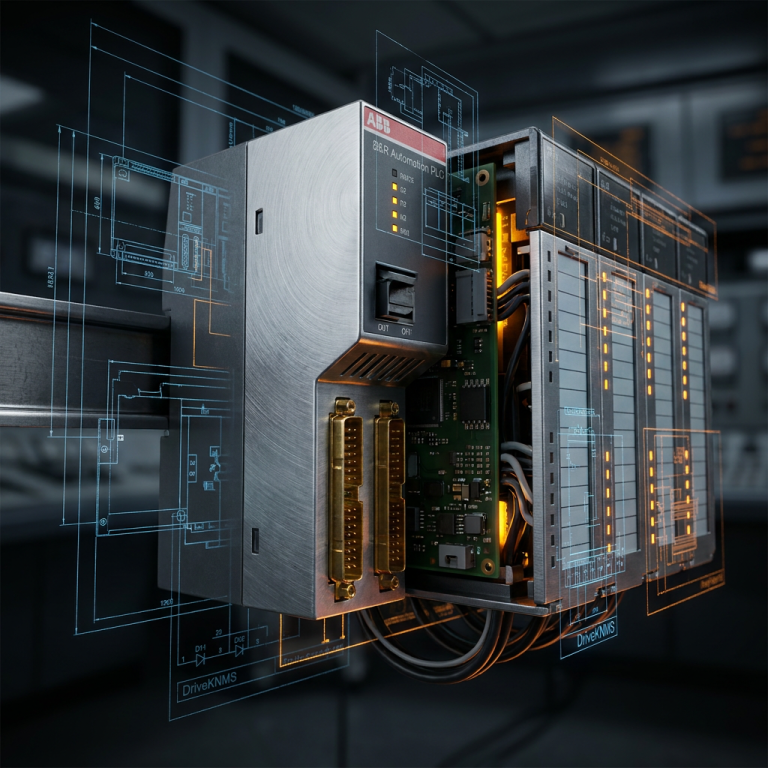
The core of the recent CISA alert involves several high-severity vulnerabilities in the ControlLogix communication modules and controller firmware. These flaws allow unauthenticated remote attackers to execute arbitrary code or trigger denial-of-service (DoS) conditions on critical infrastructure. For a plant manager or maintenance engineer, this translates to the risk of an unplanned total shutdown, or worse, the silent manipulation of process variables that could compromise equipment integrity and personnel safety.
The Hidden Risk in Legacy Spare Parts
As experts in industrial control system longevity, we at DriveKNMS see a second, often overlooked risk: the integrity of your spare parts inventory. When a vulnerability of this magnitude hits, the first response is typically to patch active controllers. However, what happens when a critical module fails three months from now, and your maintenance team pulls a legacy, unpatched spare from the shelf?
Inventorying PLC and DCS Control modules is no longer just about hardware availability; it is about firmware compliance. A spare module with outdated firmware is effectively a dormant security hole waiting to be plugged into your network. This is why we recommend a dual-track strategy: patching the active base while simultaneously auditing the firmware levels of all critical spares in the warehouse.
Actionable Steps for Maintenance Engineers
If your facility relies on the ControlLogix 5570 or 5580 series, the following steps are non-negotiable under the current threat landscape:
- Firmware Audit: Use FactoryTalk AssetCentre or manual inventory tools to identify all modules running affected firmware versions. Don’t forget communication adapters like the 1756-EN2T or 1756-EN3TR.
- Network Segmentation: Ensure that all PLC hardware is isolated from the business network and the public internet. The CISA advisory highlights that many exploitations occur via poorly configured remote access points.
- Spare Part Lifecycle Management: Before purchasing new or refurbished modules, verify the firmware capabilities. If you are sourcing Monitoring Systems or PLC modules to maintain an aging system, ensure your supplier provides detailed hardware revision data.
Conclusion: Resiliency Over Reactivity
The industrial sector can no longer afford to treat cybersecurity as a “nice-to-have” IT function. When active exploits target the physical controllers responsible for production, security becomes a core component of plant uptime. By following the 2026 CISA directives and maintaining a secure, audited inventory of Rockwell spares, you ensure that your facility remains resilient against both mechanical failure and digital threats.
Frequently Asked Questions
Q: Does this CISA advisory apply to my older SLC 500 or PLC-5 systems?
A: While the current exploit specifically targets the ControlLogix family, the trend shows that legacy systems are increasingly targeted because they lack modern encryption. While not explicitly in this KEV list, SLC 500 systems should be air-gapped as a primary defense.
Q: Can I patch my firmware without taking the process offline?
A: Most ControlLogix firmware updates require the controller to be in Program mode, which stops the logic execution. We recommend scheduling these updates during the next planned maintenance window or using a redundant chassis setup to minimize downtime.
Q: How do I know if the refurbished spares I buy are secure?
A: Always source from reputable partners who provide revision history. At DriveKNMS, we emphasize the importance of matching hardware revisions to your specific environmental requirements to ensure both security and compatibility.
Q: What is the risk if I ignore the May 2026 deadline?
A: Beyond the risk of a cyberattack, many industrial insurance policies are updated to reflect CISA KEV mandates. Failure to comply can lead to denied claims in the event of an outage or data breach.
DriveKNMS Consulting: Request a Quote from our engineers for specific module compatibility and secure sourcing of industrial automation hardware. We help you extend the life of your critical systems while meeting modern security standards.
© 2026 DriveKNMS. All rights reserved.
Official Website: https://driveknms.com
Inquiry: [email protected] | WhatsApp/Tel: +86 18359293191