As we navigate the second quarter of 2026, the industrial automation landscape is facing a familiar yet intensified challenge: the collision of legacy hardware stability with modern cybersecurity mandates. On May 12, 2026, the industrial world saw a significant wave of security advisories, with Siemens and CISA releasing critical updates for the SIMATIC S7 family. For maintenance engineers and procurement managers responsible for aging facilities, these advisories are more than just technical bulletins—they are strategic signals that impact how we manage, source, and maintain our critical spare parts inventory.
The May 2026 Siemens Security Landscape
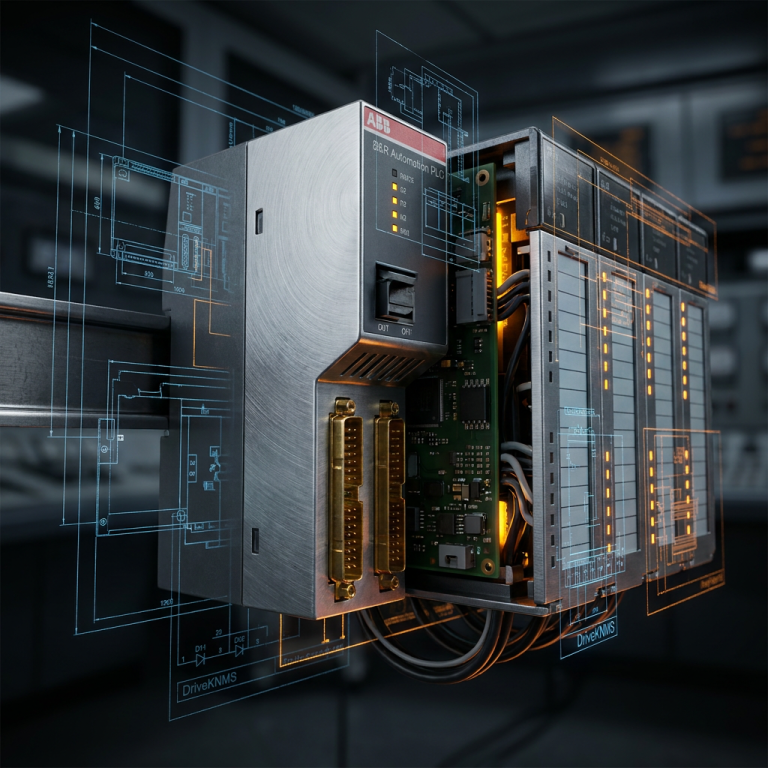
The latest “Patch Tuesday” from Siemens has brought several high-severity vulnerabilities to light, particularly affecting the communication processors and firmware of the S7-1200 and S7-1500 series. While these are modern systems, the “halo effect” of these vulnerabilities often extends to legacy migrations. Many facilities running Siemens SIMATIC S7-300 and S7-400 hardware are currently in the middle of long-term phase-outs or hybrid integration projects where legacy racks communicate with newer S7-1500 controllers. A vulnerability in the newer tier can inadvertently expose the older, less secure legacy tier if network segmentation is not rigorously maintained.
CISA’s involvement in these May 2026 advisories adds a layer of regulatory weight. When a vulnerability is added to the Known Exploited Vulnerabilities (KEV) catalog, it isn’t just a recommendation to patch; it is an alert that actors are actively seeking out these specific entry points. For plants operating 24/7, the dilemma is clear: do you risk the downtime of a firmware flash, or do you risk the potentially catastrophic downtime of a security breach?
The Longevity Paradox: Maintenance vs. Security
At DriveKNMS, we often speak with engineers who are hesitant to touch a system that has been running reliably for fifteen years. “If it isn’t broken, don’t fix it” is a mantra that has saved many production lines from botched updates. However, the 2026 security environment is redefining what “broken” means. A system with an unpatched remote code execution flaw is technically “broken” from a risk management perspective, even if the motors are still turning.
The paradox lies in the hardware. Older SIMATIC modules were designed for a world where the “air gap” was a physical reality. Today, even isolated systems often have indirect connections through maintenance laptops, industrial gateways, or remote access solutions. The 2026 advisories highlight that the “perimeter” of the PLC is no longer the cabinet door—it is every packet that reaches the backplane.
Strategic Spare Parts Management in a Vulnerable World
One of the most critical but overlooked aspects of these security waves is the integrity of the spare parts warehouse. Imagine a scenario where a Siemens S7-1500 CPU fails at 2:00 AM. The on-call technician pulls a spare from the shelf, installs it, and restores the program. If that spare has been sitting on the shelf since 2024, it likely carries the very vulnerabilities that CISA just warned about. You have effectively “un-patched” your system in the middle of a repair.
To combat this, we recommend a “Secure Spares Audit”:
- Firmware Verification: Document the firmware version of every Siemens module in your inventory. For S7-1500 and S7-1200, ensure they can be flashed to the latest May 2026 revisions if needed.
- Legacy Air-Gapping: For older Monitoring Systems and S7-300 racks that cannot be patched, focus on physical and logical isolation. If the hardware can’t be made secure, the network must be.
- Sourcing Revision-Specific Spares: When purchasing replacement parts for obsolete systems, don’t just look at the part number. Look at the hardware and firmware revision. Working with a specialist who understands these nuances is the difference between a successful repair and a security incident.
Moving Forward: The DriveKNMS Perspective
As we help our clients manage the lifecycle of their industrial automation hardware, we see that the most resilient facilities are those that treat security as a part of their maintenance schedule, not an IT afterthought. The Siemens S7 advisories of May 2026 are a reminder that even the most trusted hardware requires a proactive management strategy. Whether you are maintaining a legacy 800xA system or a modern SIMATIC plant, the goal remains the same: maximum uptime with minimum risk.
Frequently Asked Questions
Q: Are my legacy Siemens S7-300 modules affected by the May 2026 advisories?
A: Most of the recent critical advisories focus on the newer S7-1200 and S7-1500 families. However, if your S7-300 is networked with these newer systems, it can be at risk through lateral movement. We recommend a full network audit for all legacy S7 hardware.
Q: Can I flash firmware on older S7 modules to fix security flaws?
A: For newer generations, yes. For older “Classic” S7 modules, many vulnerabilities are inherent to the hardware design and cannot be patched. In these cases, air-gapping and industrial firewalls are your best defense.
Q: How do I know the firmware version of the spares I buy from DriveKNMS?
A: We provide detailed information on the hardware revisions of the parts we source. Our goal is to ensure that the spares you receive match your system’s technical and security requirements.
Q: What happens if I ignore the CISA KEV deadlines for these Siemens patches?
A: Beyond the immediate risk of a cyberattack, failure to comply with CISA directives can impact your facility’s cyber-insurance coverage and may lead to regulatory penalties for critical infrastructure providers.
DriveKNMS Consulting: Request a Quote for your Siemens SIMATIC spare part requirements. Our engineering team is dedicated to helping you extend the life of your systems while maintaining the highest standards of industrial security.
© 2026 DriveKNMS. All rights reserved.
Official Website: https://driveknms.com
Inquiry: [email protected] | WhatsApp/Tel: +86 18359293191